Trezor Login: The Complete Guide for Crypto Users
Secure, simple, and beginner-friendly ways to access your Trezor wallet safely
What is Trezor and Why Login Security Matters
Trezor is one of the most trusted hardware wallets in the crypto world. Think of it as a digital safe for your Bitcoin, Ethereum, and other cryptocurrencies. Unlike software wallets, Trezor stores your private keys offline, meaning hackers cannot easily access your funds. Logging into your Trezor correctly is essential because it ensures your digital assets remain protected from phishing, malware, and unauthorized access.
Pro Tip: Always ensure you are using the official Trezor website or the official Trezor Suite app to log in. Avoid links from emails or social media—they could be phishing attempts!
Step-by-Step Trezor Login Process
Step 1: Connect Your Trezor Device
Plug your Trezor device into your computer using the provided USB cable. Once connected, the device will power on and display the Trezor logo.
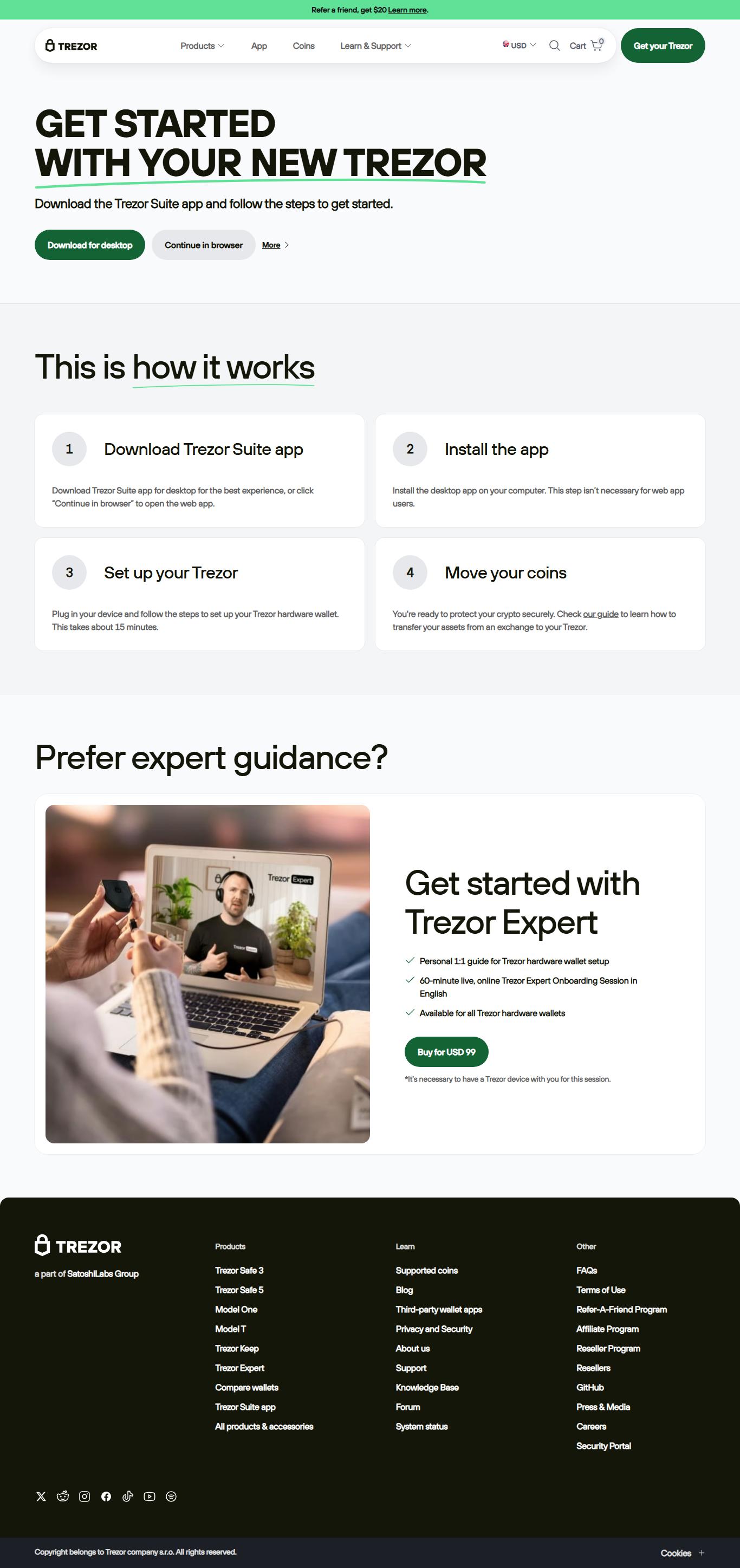
Step 2: Open Trezor Suite
Launch the Trezor Suite application on your desktop or use the official web version. This app acts as a bridge between your hardware wallet and your cryptocurrencies.
Step 3: Enter Your PIN
Your Trezor device will prompt you to enter your PIN. Unlike typical keyboards, the PIN entry is randomized on the screen for extra security, reducing the risk of keylogging attacks.
Step 4: Access Your Wallet
Once your PIN is accepted, your Trezor wallet dashboard appears in the Suite. You can now view balances, send crypto, and check transaction history safely.
Common Issues During Trezor Login
- Device not recognized: Try a different USB port or cable. Ensure your device firmware is up to date.
- Forgot PIN: If you forget your PIN, your wallet can still be recovered using the recovery seed (the 24-word backup phrase you received when initializing Trezor).
- Browser compatibility: Trezor works best on Chrome, Brave, or Firefox. Disable browser extensions that might interfere with Trezor Suite.
Understanding Trezor Security Features
Trezor isn’t just a USB stick; it’s packed with advanced security features that make crypto management safe for both beginners and experienced users:
PIN Protection
Ensures only authorized users can unlock the device. Randomized PIN entry prevents shoulder-surfing and malware attacks.
Recovery Seed
A 24-word phrase that can restore your wallet in case of loss or damage. Keep it offline and secure.
Firmware Verification
Each time your device starts, it checks its firmware integrity to prevent tampering and malware injection.
Trezor Login vs. Software Wallet Login
| Feature | Trezor Login | Software Wallet Login |
|---|---|---|
| Security | Offline keys, PIN, and recovery seed | Online keys, more vulnerable to hacks |
| Ease of Use | Slightly more steps but very secure | Simple login with password |
| Recovery Options | 24-word seed phrase | Password reset (if email linked) |
| Cost | Paid hardware device | Free software |
Frequently Asked Questions About Trezor Login
Q1: Can I log in to Trezor without the device?
A1: No. Trezor requires the hardware device to authenticate. Your private keys never leave the device.
Q2: What happens if I lose my Trezor?
A2: You can restore your wallet on a new Trezor or compatible wallet using your recovery seed. This is why keeping it safe offline is critical.
Q3: How often should I update my firmware?
A3: Regular updates are recommended. They ensure the device is protected against the latest vulnerabilities.
Conclusion: Mastering Your Trezor Login
Logging into your Trezor wallet is the gateway to secure crypto management. By understanding the PIN system, recovery seed, and device authentication, you ensure your digital assets stay protected. Whether you are a beginner or a seasoned investor, following the correct Trezor login steps builds confidence and safety in your crypto journey.
Remember: your crypto security starts with a safe and verified login.